Creating informational website for deployment hybrid infrastructure
MINISTRY OF EDUCATION AND
SCIENCE OF THE REPUBLIC OF KAZAKHSTAN
INTERNATIONAL INFORMATION
TECHNOLOGY UNIVERSITY JSC
FACULTY OF INFORMATION
TECHNOLOGY
Melisuly
D.
informational website for
deployment hybrid infrastructurePROJECT
Major 5B070400 - Computer science and software engineering
2015
MINISTRY OF EDUCATION AND
SCIENCE OF THE REPUBLIC OF KAZAKHSTAN
INTERNATIONAL INFORMATION
TECHNOLOGY UNIVERSITY JSC
FACULTY OF INFORMATION
TECHNOLOGY
Department of Computer
Science, Software Engineering and Telecommunication
APPROVED
FOR DEFENCEof the Department,.Sc.Eng., Professor
_________R.Muhamediyev
«_____» ___________2015
PROJECT
Topic: Creating
informational website for deployment hybrid infrastructure
STUDENT: CSSE111, Melisuly D.:.t.sc.
assoc. prof.,G.I.:
c.t.sc.
assoc. prof.,V.Z
2015
MINISTRY
OF EDUCATION AND SCIENCE OF THE REPUBLIC OF KAZAKHSTAN
INTERNATIONAL
INFORMATION TECHNOLOGY UNIVERSITY JSC
FACULTY
OF INFORMATION TECHNOLOGYof Computer Science, Software Engineering and
Telecommunication
Major
5B070400 - Computer Science
and Software Engineering
of the Department,.Sc.Eng., Professor
___________R.Muhamediyev «_____» ___________201_PROJECT
ASSIGNMENT
________________________Melisuly_Dauren_______________________
(student name)
. Diploma project topic
___________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________by IITU order № dated «____» _______________ 201
2. Assignment submission deadline _____________________________
3. Initial data ______________________________________________
_________________________________________________________________________________________________________________________________________________________________________________________________
. List of issues to be developed _______________________________
____________________________________________________________________________________________________________________________
5. Laser disc containing the diploma paper text with attachments _____________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________
6. Project consultants, by sections
|
Section
|
Consultant
|
Signature, date
|
|
|
Assigned by
|
Received by
|
|
Economic part
|
Berdykulova G.M
|
|
|
|
Occupational safety and health
|
Nurmuhanbetova G.A
|
|
|
|
English translation
|
Zhaparova A.A
|
|
|
|
Standardized control
|
Abdullina V.Z
|
|
|
|
|
|
|
Date of issuing the assignment ___________________________________
Supervisor____________________________________________________
(signature)by__________________________________________________
(signature)
7. DIPLOMA PROJECT WORK SCHEDULE
|
№
|
Diploma work stage
|
Date of submission
|
Comment
|
|
1 2 3 4 5 6 7
|
Review of literature and works on
the subject of cloud computing Review and analysis of work on cloud computing
Review of the theoretical part Developing applications for cloud computing
The economical part of the project Writing sections of labor protection
Explanatory work of diploma project
|
12.01.2015 - 20.01.2015 12.01.2015 - 06.02.2015 06.02.2015 - 20.02.2015 20.02.2015 - 15.03.2015
20.03.2015 - 15.04.2015 20.03.2015 - 15.04.2015 15.03.2015 - 10.05.2015
|
|
date _______________________________________________
Supervisor____________________________________________________
(signature)by_____________________________________________
(signature)
Statement
of compliance with the Professional Code of Ethics,
_____________________________, student majoring in 5В070400 - Computer Science and
Software Engineering, IITU JSC, am stating that my diploma paper on the topic:
«___________________________________________
_____________________________________________________________________________»,
submitted to the State Attestation Committee for public defence, complies with
the Professional Code of Ethics and does not contain plagiarism, falsified data
or incorrect citations.am fully aware of the fact that in accordance with the
IITU Regulation on preparation and defence of graduation papers (diploma
projects) detection of plagiarism, data falsification and incorrect citations
in my diploma paper shall constitute ground for lowering my grade or a
“Failure”.
MINISTRY OF EDUCATION AND
SCIENCE OF THE REPUBLIC OF KAZAKHSTAN
INTERNATIONAL INFORMATION
TECHNOLOGY UNIVERSITY JSC
FACULTY OF INFORMATION
TECHNOLOGIESof Computer Science, Software Engineering and Telecommunication
’S REVIEW
of the diploma project by
________________________________________in 5В070400 - Computer Science and Software
Engineering
Diploma Project Supervisor _____________________________________Project
topic: __________________________________________
__________________________________________________________
|
№
|
Qualification requirement
|
Degree of compliance
|
Recommended grade
|
Grade
|
|
1
|
Relevance and significance
|
High
|
min:0 - max:15
|
|
|
|
Medium
|
|
|
|
|
Low
|
|
|
|
|
Not topical
|
|
|
|
2
|
Novelty
|
Yes
|
min: 0- max:15
|
|
|
|
No
|
|
|
|
3
|
Practical value
|
Yes
|
min: 0- max:10
|
|
|
|
No
|
|
|
|
4
|
Correspondence to the specialist’s
training profile
|
Corresponds
|
min: 0- max:10
|
|
|
|
Not corresponds
|
|
|
|
5
|
Independence of the work done
|
Yes
|
min:0- max:10
|
|
|
|
No
|
|
|
|
6
|
Provision of conclusions and
recommendations
|
Yes
|
min:0- max:10
|
|
|
|
No
|
|
|
|
7
|
Problem-solving quality
|
High
|
min: 0- max:15
|
|
|
|
Medium
|
|
|
|
|
Low
|
|
|
|
8
|
Degree of research completion
|
High
|
min:0- max:15
|
|
|
|
Medium
|
|
|
|
|
Low
|
|
|
|
TOTAL
|
|
|
|
Comments on the diploma project:
_____________________________________________________________
Аннотация
В дипломном проекте разработано веб-приложение по созданию
гибридной инфраструктуры. Для этого проведен сравнительный анализ существующих
на рынке веб-приложении. Изучены понятия облачных вычислений, классификации,
модели развертывания, структура гибридного облака. Также были проанализированы
методы работы платформы Windows Azure, Microsoft Hyper-V 2008/2012 , VMWare.
Основываясь на собранных сведениях было разработано веб-приложение которое
помогает при использовании технологии виртуализации при создании гибридного
облако.
Ключевые слова: облачные вычисления, гибридное облако,
частное облако, публичное облако, модели и методы развертывания.
Дипломная работа содержит 70 страниц, 31 иллюстраций, 8
таблицы, 15 использованных источников.
Аңдатпа
Дипломдық жобада буданды инфрақұрылымды әзірлеуге
арналған web-қосымшасы әзірленген. Осы үшін әлемдегі
бар бұлтты есептеулермен айналысатын web-қосымшалары салыстырмалы
анализі өткізілген. Бұлтты есептеулердің ұғымы,
сыныптамалары, өрістетудің түрлері мен әдістері, бұданды
бұлттың құрылымы танып білінген. Сондай-ақ
Windows Azure Microsoft Hyper-V 2008/2012 , VMWare платформаларының жұмыс
істеу әдісі қаралған. Жинақталған ақпараттар
негізінде буданды инфрақұрылымды әзірлеуге үшін арналған
web-қосымшасы әзірленген.
Рисктердің түр әсерін жою мақсатында
бұл қосымша кез келген деңгейдегі компаниялардың
пайдалануына жарамды.
Маңызды сөздер: бұлтты есептеулер, бұданды
бұлт, дербес бұлт, көпшілік бұлт, өрістетудің
түрлері мен әдістері.
Диплом жұмысы 70 бет, 31 түрлі- түсті, 8
кесте, 15 зерттеу көздерінен тұрады.
Abstract
the diploma project the web-application for create a hybrid
infrastructure
is developed. To achieve this, a comparative analysis of the existing
web-application on the market is done. Concepts of cloud computing, classification, deployment model, the structure of
the hybrid cloud is examined. Also the working methods of
the platform Windows Azure, Microsoft Hyper-V 2008/2012, VMWare are analyzed. Based on the collected
information a web application that helps when you use virtualization technology
to create a hybrid cloud was developed: cloud
computing, hybrid cloud, private cloud, public cloud models and methods of
deployment.project
contains 70 pages, 31 illustrations, 8 tables, 15 references.
Introduction
. Technology of cloud computing
.1 Review of development of cloud computing.
.2 Service models of cloud computing.
.3 Deployment models of cloud computing.
.4 Safety of information.
. Technology of virtualization
.1 Virtualization of resources.
.2 Virtualization of platforms.
.3 Hypervisor.
. Algorithm of “Cloudy”
.1 Functional of website.
.2 Software tools.
. Safety and labor protection
. Justification of the cost-effectiveness of the
project
Introduction
Despite the fact that the term ,which
familiar to us, "cloud" services appeared in the 70s of the last
century, the last 10 years, the term has become very popular. Just at that
time, software developers have proposed a model of the application, in which
all calculations and data processing are carried out not on the user's computer
and on remote servers.who seriously interested in this technology was Amazon
company. Amazon introduced his “invention” to its customers which called like
extensive system of web services. The principal difference of the new
infrastructure was that users receive in order not only for hosting storage but
also to computing power of servers owned by Amazon. Just a year later similar
services offered other companies IT-industry: Google, Sun and IBM. A year
later, Microsoft announced not just an app - an entire operating system built
on the basis of "cloud" computing model.goal of diploma project is to
construct of an informational web site where placed the theoretical material
and arranged laboratory works which will helps to users in deployment of a
hybrid cloud which based on Windows Azure and Microsoft Server 2012 R2. And
also to improve the knowledge on a practical basis for technology, services,
and services provided by "cloud computing". To accomplish goal it is
necessary to:
The goal of diploma project is to improve information
security in cloud infrastructures. To accomplish goal it is necessary to:
) Get acquainted with the term of “cloud computing” and
make review to existing cloud solutions;
2) Classification of Cloud Computing by expansion models and web-services;
3) Define the hypervisor-based virtualization technology theory;
) Consider
the use of cloud technologies provided by Windows Azure and Windows Server
2008/2012;
) Development of the algorithm of laboratory works;
) Implementation of the program set.
1. Technology of cloud computing
computing - is a model of ensuring universal network access
on demand to a shared pool of the configured computing resources which can be
provided and introduced quickly with a minimum of administrative efforts or
interactions about service provider. Now usually understand possibility of
obtaining necessary computing capacities as cloud computing on demand from a
network, and to the user details of realization of this mechanism aren't
important and he receives from this "clouds" all necessary.cloudy
calculation is directly connected with development of computer facilities,
systems and networks of data storage, consolidation of infrastructures. Because
the centralized data processing on the basis of mainframes solves many problems
of information systems of scale of the enterprise more simply and cheaper than
the distributed processing used in personal computers, in 1994 growth of
interest in cloudy technologies began again.
1.1 Review of development of
cloud computing
main trends in the development of infrastructure solutions
which contributed to the emergence of cloud computing:
· Increased productivity of computers.
The advent of multi-processor and multi-core computing systems.Development of
blade-systems.
· The appearance of storage systems and
storage networks.
· Consolidation of infrastructure.of service of a large number of users
(the distributed databases, Internet services, hosting) and difficult
resource-intensive (scientific tasks, mathematical modeling) calculation always
demanded high concentration of computing means which needed development.
Producers of processors reached reasonable restriction of accumulation of power
of the processor, and it led to emergence of the multiprocessor and
multinuclear computing systems. According to Figure 1.1, the emergence of a
universal computer system IBM System / 360 in 1864, went down in history as the
first mainframe. Mainframe - a host computer center with large internal and
external memory.increase performance computing center was effective to increase
the number of individual computing modules, it created new types of servers - known
as Blade-servers.scheme of stages of development cloud computing is given in
figure 1.1.
Figure 1.1 - Scheme of stages of development cloudy
calculation
cloud computing algorithm virtualization
Blade-server - is a modular single-board
computer-system, containing CPU and RAM which are inserted into the special
chassis. These chassis with several blades is Blade-system. At present, leaders
in production of blade-servers are companies like: Hewlett-Packard <#"791879.files/image002.gif">
Рисунок 1.2 - Types of consolidation
to Figure 1.2 consolidation is divided into the
following types:
· Server Consolidation - Move
decentralized applications distributed on different servers of the company, in
one centralized cluster of homogeneous servers;
· • Consolidation of storage systems -
sharing a centralized storage system several heterogeneous nodes;
· Application consolidation -
accommodation of multiple applications on the same host.accordance with Figure
1.3 ,a cloud is based on consolidated at least one server and at least one data
storage system combined with the help of topologies of SAN.

Figure 1.3 - Server and system of data storage.
1.2 Service models of cloud
computing
Cloud computing - hardware and software available to users
through the Internet or a local area network in the form of different types of
service (web service), allowing the use of user-friendly interface for remote
access to selected resources. In accordance with Figure 1.4 shows the services
provided by cloud computing.
Рисунок
1.4 - Типы облачных вычислении
to Figure 1.4, cloud computing provides the following web
services:
· IaaS - Infrastructure as a service;
· Paas - Platform as a service;
· SaaS - Software as a service;
· HaaS - Hardware as a Service;
· WaaS - Workplace as a Service;
· DaaS - Data as a Service;
· SECaaS - Security as a Service;
1.2.1 Infrastructure
as a service(IaaS)
IaaS (Infrastructure as a Service) -
is a service of rent virtual servers are cost-effective way to provide modern
and efficient enterprise computing resources.in the data center cloud solutions
“IaaS” provide customers with the development and maintenance, rapid expansion
or reduction of the required IT-systems according to the needs of the
enterprise without investing in the development and maintenance of the server
system.
IaaS vendors provide components of the following levels:
· Virtualization platforms for
launching virtual machines
· Hardware (usually Grid with massive
horizontal scalability);
· A computer network (including
routers, firewalls, load balancing, etc.);of buying space in data centers,
servers, software, network equipment, etc. Clients of IaaS rent the resources
that are on the side serving providers IaaS. Payment for services is usually
done on a monthly basis. User pays only for consumed resources. The main
advantages of this type includes:
· Free access to a
pre-configured environment;
· Using the infrastructure
of the last generation;
· Protected and isolated
computing platforms;
· Reduced risk through the
use of third-party resources maintained by third parties;
· The ability to manage peak
loads;
· Less time, cost and
complexity is added or enhanced functionality.technologies of virtualization of
infrastructure (in our case IaaS) allow you to implement all the functionality
on a single platform that allows the necessary IT infrastructure outsourcing business
units. This may be a virtual server for hosting several dozen sites, and can be
a full-fledged corporate infrastructure of dozens of servers including virtual
employees' desktops, mail server, IP-telephony, CRM system and document
management server databases, and etc.who use IaaS was Amazon company.
Among the companies providing IaaS can be noted GoGrid which
has a very user friendly interface to manage the VPS, and cloud storage with
support for protocols SCP, FTP, SAMBA / CIFS, RSYNC.
“Enomaly” is a solution for deploying and managing virtual
applications in the cloud. Among the supported virtual architectures: Linux,
Windows, Solaris and BSD Guests. Virtualization is used not only Xen, and KVM,
and VMware.
Cloud computing environment can be created on the basis of
cloud solutions Amazon EC2, IBM x86, Microsoft Azure, EMC, VMware, based on
open-SOURCE solutions OpenStack, RackSpace based on OpenStack et al., Which
allow to transform the data center into a dynamic IT environment. Moreover,
cloud computing cloud database used, i.e. databases that run on cloud computing
platforms. As a cloud-based database used as an SQL-oriented model and data
model NoSQL.
1.2.2 Software as a service
(SaaS)
SaaS (software as a service also software on demand) - business model of using and
selling of software where supplier develop web-application and manage by
herself, providing customers with access to the software via the Internet. The
main advantage of the SaaS model for the consumer is the absence of costs associated
with installing, upgrading and support of the equipment and working on it
software. In other words SaaS applications are installed and run on the server
SaaS-provider, and users can access them through a web browser and entering the
data, the user is ready results through the Internet and use them.delivered the
following types of cloud applications and services: Business Apps, Office Web
Apps, Management Apps, Communications, Security and etc. The most popular cloud
applications are: CRM (Customer Relationship Management), HRM (Human resources management),
ERP (Enterprise Resource Planning, for example: 1С), office application, communication tools and etc.
Salesforce.com is the world's largest provider of cloud-based CRM. Along with
services whih is describes above, SaaS services include data backup “Online
Backup”. At a certain time service automatically encrypts data on a computer or
other device and send them to a remote server. Thanks to this, the data can be
accessed from anywhere on Earth. This service now provides a variety of
companies, including such as Nero and Symantec.
Main software application:
§ Office Web Apps (Google
Docs, Office Online/Microsoft OneDrive, etc.),
§ Business Apps (CMR, FRM,
IBM® B2B Cloud Services, Axway Cloud B2B, amoCRM SaaS service for B2B, Google
Apps for Business),
§ Management Apps (ERP/АРЕНДА 1С, HRM, SCM, MRP),
§ Communications (Gmail,
Google Hangouts, Microsoft Lync Online, Cloud PBX or cloudy АТС, MDM),
§ Security (Panda Cloud
Email Protection, Panda Cloud Internet Protection, McAfee SaaS Email Protection
& Continuity, Сomfortway Mobile
Security), and etc.
1.2.3 Platform as a Service (PaaS)
The development of "cloud" computing has led to
platforms that allow you to create and run a web application. Platform as a Service
(PaaS) - is to provide an integrated platform for development, testing,
deployment and support of web applications as a service organized on the basis
of the concept of cloud computing.this model, the entire information technology
infrastructure, including computer networks, servers, storage, entirely
controlled by the provider. Provider defines a set of available types of
consumer platforms, and a set of controlled parameters platforms, and the
consumer is given the opportunity to use the platform to create their virtual
copies, install, develop, test, operate on them, application software, and the
dynamically changing the amount of consumed computing resources. PaaS model
envisages that a provider of cloud services provides customers with programming
languages, development environment, libraries, services and tools, with which
the end user develops and deploys the application. Figure 1.5 shows services
which provide PaaS.
 1.5
- Services offered by PaaS
1.5
- Services offered by PaaS
to figure 1.5 PaaS provides a software platform and
maintenance as a service composed of:
§ OS - network operating
system (Unix-systems, including Ubuntu Server, BSD/OS Family, Solaris/SunOS and
etc. or Windows Server)
§ Database - database
management system(DBMS) (MySQL, Microsoft SQL, SQL Database, PostgreSQL, Oracle
and etc.)
§ Middleware - software
middle layer or binding (intermediate) software, which is designed to ensure
interoperability between different applications, systems and components.
§ Software development tools
and testing - software tools for developing and testing web applications
(software development environment: software frameworks, libraries, etc.
programming languages to create a web application: Python, Java, PHP, Ruby, JS
for Node.js, etc.).
§ App server - application
server for developing, testing, debugging and web applications.services provide
a large number of companies such as Microsoft, Amazon.com, Google. PaaS model
based on the license or subscription model so users only pay for what they use.
PaaS include workflows for creating, development, testing, deployment and
placement of application. Also, application services, virtual offices, database
integration, security, scalability, storage, wealth management, tools,
dashboards, and more.Microsoft Windows Azure- a group of "cloud"
technologies, each of which provides a specific set of services for application
developers. Computing services of Windows Azure works on basis of Windows. In
addition to applications which developed on the platform ".NET
Framework" Windows Azure also allows developers to run applications in the
languages of Windows - C #, Visual Basic, C ++ and other - using Visual Studio
or other development tools. Developers can create web applications using
technologies such as ASP.NET and Windows Communication Foundation (WCF),
applications that run as independent background processes or applications that
combine both.
1.3
Deployment models of cloud computing
addition to the various ways of providing services as SaaS,
PaaS and IaaS, and others, there are several options for the deployment of
cloud systems, as shown in Figure 1.6.
 1.6
- Deployment models and Web services of cloud computing
1.6
- Deployment models and Web services of cloud computing
cloud computing algorithm virtualization
According to Figure 1.6 deployment models of cloud computing
are divided into:
· Private cloud
· Public cloud
· Hybrid cloud
1.3.1 Private cloud
Private cloud - cloud infrastructure intended for use by a
single organization. Private cloud covers the need for IT services
organization, its divisions or departments , clients, contractors and others.
Private cloud (usually) physically located and is in the ownership, management
and operation of the organization of the owner.
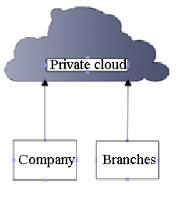
Figure 1.7 - Private cloud
to the needs private cloud allows to flexibly redistribute
computing capacity and a load of shared infrastructure to ensure optimal
performance and required reliability. Tools for monitoring and control allow IT
professionals to track the use of hardware resources within the organization,
predict and optimize the load.well as other types of clouds, private clouds
have their advantages and disadvantages which we can see in Table 1.1.
Table 1.1 Advantages and
disadvantages of private cloud
|
Advantages
|
Disadvantages
|
|
Control, management and
configurability cloud environments
|
Significant costs
|
|
High performance
|
The risk of losing working capacity
services because of physical threats
|
|
Security
|
Limited resources
|
|
Efficiency of the IT department
|
|
As shown in Table 1.1 private clouds
have their own advantages and disadvantages. The benefits of private clouds
include the following features:
· More control in comparison
with public cloud at the expense of that all the components of the IT
infrastructure placed in the organization of consumer. Thus, companies can
monitor and manage cloud environments more efficiently. High level of security
provided by the fact that the service consumer is one single organization, so
that the entire infrastructure can be optimally configured for the existing
data protection requirements.
· High performance private
cloud associated in particular with the fact that they operate within the
framework of internal firewalls and protection perimeter of the corporate
network, so data transfer is much faster. Configurability of private clouds
also remains at a high level.
· Implementation of private
cloud increases the efficiency of the IT department - at any time at the
request of the business can deploy the necessary service for 5-10 minutes. IT
team only raise a virtual machine from a template and install the necessary
service, at a time when companies with traditional IT infrastructure would have
to order a server, install it on software and applications, and connect it to
the network. Only one installation of equipment sometimes takes 6-8 weeks.of
private cloud are following factors:
· Significant costs at all
stages of the life cycle of clouds, from implementation to supporting the
working capacity. At the stage of deployment requires investment in equipment
and software. Also need to manage a private cloud, which also entails
administration costs and attract qualified IT professionals.
· In comparison with the
public cloud there are risks of loss of working capacity of cloud services and
data loss because of physical threats of infrastructure.
· Sooner or later,
organization which use private cloud may face when resourses of cloud
infrastructure may be not enough.
1.3.2 Public cloud
Public cloud - infrastructure for
free use by the public. Public cloud may be in the ownership, management and
operation of commercial, academic and government organizations (or any
combination thereof). Public cloud physically exists in the jurisdiction of the
owner - the service provider.the structure, as well as private clouds, public
clouds have advantages and disadvantages.
Table 1.2 - Main characteristics of public clouds
|
Advantages
|
Disadvantages
|
|
The simplicity and efficiency of
use.
|
Lack of opportunities for the
control by organization.
|
|
Access to applications requiring
only an Internet connection.
|
In some cases, data transmission
may be slow.
|
|
Absence of expenditures on
"iron" and software.
|
Weak data security
|
|
Flexibility and Scalability
|
|
|
Reduced time for maintenance of
infrastructure
|
|
to the Table 1.2 pros my include
following:
· Public cloud services are
characterized by a great ease of use and efficiency,
· Access to the application
does not require anything other than a stable internet connection,
· The use of public cloud -
a real opportunity to reduce IT budget due to lack of spending on
"hardware" and software,
· Flexibility and
scalability: a model pay-as-you-go allows you to pay just as many resources as
you want at the moment, and quickly adjust this setting upward or downward,
· Abbreviation of time for
service of infrastructure: standard, not a cloud, environment change the
settings of applications or servers can take hours, days or even weeks, in a
virtual environment is much faster - in a matter of minutes,
· server applications are in
the cloud, that‘s why there are no risk of downtime of business processes due
to server crashes. Virtual server providers often configured on a powerful
physical base, located in large data centers where possible downtime counted in
minutes per year,
· The use of public clouds
and no contact users with complex computer equipment allows you to refuse the
services of IT professionals in your organization,
· Lack of long-term
contracts and mutual obligations with IT companies allows you to change the
cloud provider as needed.cons of public clouds include:
• The main disadvantage of
public cloud is the lack of options for the control of the organization:
performance of services is completely subordinated to the provider that
provides cloud technology.
· Slow speed: performance of
public cloud services depends on the stability and breadth of Internet
connection bandwidth, in some cases, data transmission may be slow. When
operating with large volumes of data public clouds can not compete with private
performance.
· Investments in IT
infrastructure among others are also an investment in the case of public cloud
investment with the future in mind is simply impossible, tangible assets are
not purchased.
· Weak data security -
another characteristic of public cloud environments. Whatever efforts did not
make the provider in the field of security, the protection of private cloud
will always be an order of magnitude more reliable.
1.3.3 Hybrid cloud
Hybrid cloud - is a combination of two or more different
cloud infrastructures (private, public) that remain unique entities but linked
by standardized or proprietary technology and data applications (eg, short-term
use of public cloud resources for load balancing between clouds)
 1.8 -Structure of hybrid cloud
1.8 -Structure of hybrid cloud
basic idea of the hybrid cloud is that when their own
capacity is not enough, the enterprise may use external resources, without
opening the data structures which remain inside. This leads to the fact that
the number of resources increases, and internal control applications using
those resources considerably increases.
1.4 Safety of
information
who are thinking about moving to cloud infrastructure,
concerned about the issue of security. On security assurances to construct the
whole marketing activity provider. And therefore the company to devote big
effort to the case such as data encryption, network traffic, backups. Just to
protect data from hackers are network intrusion detection systems, anti-virus
protection, different types of data encryption, and etc. When a user or company
move to cloud technologies are encouraged to review how the safety standards
should be, and which safety procedures performs provider of cloud technology.
Safety of stored data is performed via the use of encryption technology. The
provider should always encrypt the information stored on their servers customer
information for prevention of unauthorized access. Attackers can gain access to
information or personal data cloud services in different ways, as shown in
Figure 1.9.
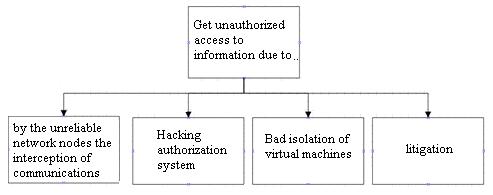 1.9 - Methods of unauthorized access
to information
1.9 - Methods of unauthorized access
to information
to the scheme of unauthorized access to information, an
attacker can obtain information through:
• unreliable nodes in the network to intercept data
• hacking authorization system
• due to poor insulation of virtual machines
• Due to the lawsuit where the plaintiff has access to all
servers belonging to cloud providers.order to prevent interception of data over
unreliable networks nodes, transmission data must always be encrypted and
descrypted only after user authentication. This approach ensures that the data
will not be able to edit or read any one person, even if they gain access to
them through unreliable nodes in the network. These technologies have been
developed for "thousands of man-years" and led to the creation of
reliable protocols and algorithms (such as TLS, IPsec and AES). Providers
should use these protocols, and not invent your own.most common method of
authentication is the password protection. However, service providers seeking
to offer their customers higher reliability, resort to more powerful tools,
such as certificates and tokens. Along with the use of more reliable means of
authentication to cracking providers must be able to work with such standards
as LDAP and SAML. This is necessary to ensure interoperability provider with
the system user authentication client authorization and determining the powers
granted to the user. Thanks to this provider will always have current
information about the logged in user. Worst case - when the customer provides a
specific provider a list of authorized users. As a rule, in this case, when an
employee leaves or move it to another position may be difficult. Some providers
put data of all clients in a single software environment and due to changes in
its code, trying to isolate the data of customers from each other. This
approach is reckless and unreliable. First, the attacker can find a gap in the
non-standard code that will allow him to gain access to data that he should not
see. Secondly, the error code may cause one customer accidentally "see"
other data. In recent years, there were also those other cases. Therefore, to
distinguish between user data use different virtual machines and virtual
networks is a smart move.best option when customers use each individual virtual
machine and virtual network. Separation between VM and consequently between the
users, provides hypervisor. Virtual networks, in turn, are deployed using
standard technologies such as VLAN (VirtualLocalAreaNetwork), VPLS
(VirtualPrivateLANService) and VPN (VirtualPrivateNetwork).incident when the
incident involving his clients, such as litigation or processes requiring
access to all servers, summons must cover a narrow range of issues and should
not affect other users. . But if the user does not know that there is a court
summons and a case scenario is that the user can protect only the full data
encryption. The agenda may require that the cloud provider is provided by the
court data and access to them, but the provider will not be the access key and
the key for decryption. To get one, the court will have to ask the user and
send him a summons. As a result, the user will have the same level of control
over their data in the cloud, as in your own private data center.prevent
unauthorized access cases, the provider must encrypt stored on their servers
the client's information. The provider must also permanently delete data when
they are no longer needed and will not be required in the future.
2. Virtualization technology
technology is a key element in the concept of
"cloud" computing. Virtualization technology is a key element in the
concept of "cloud" computing. Due to virtualization technologies
physical server can allocate server resources between applications, each
application "thinks" that it have a dedicated server,in this case
implemented a "one server - multiple applications", but without
sacrificing performance, availability, and security server applications.- is to
provide a set of computing resources or their logical association abstracted
from the hardware implementation, and ensure the logical isolation of computing
processes running on a single physical resource. Virtualisation means running
on the same physical machine (computer) multiple virtual machines (computers).
Figure 2.1 shows a diagram where virtualization on a single physical machine to
run multiple virtual computers.

Figure 2.1 - Visualization of virtualization
To date, suppliers of virtualization technologies offer a
reliable and manageable platform, and the market for these technologies is
booming. According to leading experts, virtualization is now one of the three
most advanced computer technology. Figure 2.2 shows the main types of
virtualization.
Рисунок 2.2 - Types of virtualization
to Figure 2.2, virtualization divided into two
fundamentally different categories:
• Virtualization platforms (creating emulators
platforms, OS virtualization and OS instances, application virtualization)
• Resource virtualization (consolidation and
aggregation of resources distributed computing, clustering computers, resource
sharing, encapsulation).Virtualization platforms or virtualization understand
the creation of software systems based on existing software and hardware.
System that provides hardware resources and software is called the host (host),
and it simulated system - guest (guest). To guest systems can run stably on the
platform of the host system, it is necessary that the software and hardware of
the host is strong enough to provide the necessary set of interfaces for access
to its resources. Each current form virtualization made its approach to the
concept of "virtualization". Types of virtualization platforms depend
on how well the simulation is carried out hardware.
2.1 Virtualization of
resources
of virtualization virtualization platforms considered
in the narrow sense, is mainly used in the process of creating virtual
machines.
Сoncept of virtualization platforms
considered in the narrow sense, is mainly used in the process of creating
virtual machines. Virtualization allows you to concentrate, to abstract and
simplify the management of groups of resources, such as network, storage, and
namespace.
The figure 2.3 shows the types of
virtualization of resources.
Figure 2.3 - types of virtualization of resorces
to Figure 2.3 virtualization of resources can be
divided into the foll owing types.
· Association,aggregation
and concentration of components;
· Grid computing;
· Partitioning;
· Encapsulation.
Under the guise of virtualization
'Association, aggregation and concentration of components "refers to the
organization of multiple physical or logical objects in the resource pools
(groups), is a convenient user interface. Examples of this type of
virtualization:
· Multiprocessor system
appears to us as one powerful system,
· RAID-massives and
management tools of volume, which combine a multiple physical discs into form
of one logical,
· Storage virtualization
used in the construction of storage area network (SAN)
· Virtual Private Network
(VPN) and Network Address Translation (NAT) allows you to create virtual space
network addresses and names.of virtualization which calls “grid computing
include techniques used by combining a plurality of individual computers in the
global system (metacomputer) jointly solving the general problem.In the process
of virtualization is a division of a single large resource for several similar
objects, easy-to-use. In the storage area network is called zoning resources
(«zoning»).
“Encapsulation” in relation to
virtualization, we can say that the process of creating a system that provides
a user-friendly interface to work with her and hides the details of the
complexity of its implementation. For example, the use of the CPU cache to
speed up the computation is not reflected in its external interfaces.
2.2
Virtualization of platforms
Types of virtualization platforms depend on how well the
simulation is carried out hardware. There is still no uniform agreement about
the terms in the field of virtualization. As shown in Figure 2.4
virtualization of platform is divided into the following categories:
· Full emulation
(simulation)
· Paravirtualization
· Application level
virtualization
· Operating system-level
virtualization
· Virtualization address space
Рисунок 2.4 - Types of virtualization of platform
system-level virtualization -
virtualization technique, in which the operating system kernel supports
multiple isolated instances of user-space, instead of one. These items (often
referred to as containers or zones) from a user perspective is completely
identical to the real server. For systems based on UNIX, this technology can be
seen as an improved implementation of the mechanism chroot. The kernel provides
complete isolation of containers, so the program from different containers
cannot affect each other. The essence of this type of virtualization is the
virtualization of the physical server at the operating system in order to
create a more secure virtualized servers on a single physical. Guest system, in
this case, the shared use of the host operating system kernel with other
guests. A virtual machine is an environment for applications that run in
isolation. This type of virtualization is used in the organization of systems
hosting, when a single instance of the need to support multiple virtual servers
clients. Examples of OS-level virtualization: Linux-VServer, Virtuozzo, OpenVZ,
Solaris Containers and FreeBSD Jails.applying no need paravirtualized simulate
hardware but instead (or in addition), a special application programming
interface (API) for interacting with the guest operating system. This approach
requires the modification of the guest code that, in terms of community, Open
Source is not so critical. Paravirtualization system also has its hypervisor,
and API-calls to the guest system, called «hypercalls» (hypercalls). Currently,
providers are paravirtualization of XenSource and Virtual Iron.
“Application-level virtualization”
type is not like all the others, if in the previous cases are virtual
environments or virtual machines that are used for insulation applications, in
this case, the application itself is placed in a container with the necessary
elements for its operation: registry files, configuration files, and user
system objects. The result is an application that does not require the
installation on the same platform. When you transfer this application to
another machine and run it, the virtual environment created for the program,
resolves conflicts between it and the operating system, as well as other
applications. Such a method of virtualization is similar to the behavior of
interpreters of different programming languages (no wonder the
interpreter, virtual machine Java (JVM), also falls into this category).
Examples of this approach are: Thinstall, Altiris, Trigence, Softricity.full
emulation (simulation) virtual machine is fully virtualizes all hardware while
maintaining the guest operating system intact. This approach allows you to
emulate various hardware architectures.the partial emulation (native
virtualization) virtual machine virtualizes only the necessary amount of
hardware that it can be run in isolation. This approach allows you to run guest
operating systems developed only for the same architecture as that of the host.
This type of virtualization can significantly increase the performance of guest
systems compared with full emulation and is widely used at present. In
addition, in order to improve performance in virtualization platforms that use this
approach uses a special "layer" (hypervisor) between the guest
operating system and hardware that allows the guest direct access to hardware
resources. Hypervisor, also called "virtual machine monitor» (Virtual
Machine Monitor) - one of the key concepts in the world of virtualization. The
use of a hypervisor, is the link between guests and equipment, significantly
increases the speed of the platform, bringing it closer to the speed of
physical platform. The disadvantages of this type of virtualization can be
attributed dependence of virtual machines on the architecture of the hardware
platform.of products for native virtualization: VMware Workstation, VMware
Server, VMware ESX Server, Virtual Iron, Virtual PC, VirtualBox, Parallels
Desktop, and others.
2.3
Hypervisor
- in some way is minimal operating
system. It provides a running under its operating system service virtual
machine, virtualizing or emulating the (physical) hardware specific machine and
manage virtual machines, allocating and freeing resources for them. The
hypervisor provides isolation of operating systems from each other, defense and
security division of resources between the various operating systems running
and management of resources. The hypervisor provides an isolated environment for
each virtual machine, and that it provides a guest OS access to computer
hardware, as shown in Figure 2.5.

Рисунок 2.5 - Location of hypervisor
· According to the running method,
hypervisors can be divided into three types, as shown in Figure 2.6:
· 1-rst type of hypervisor (established
on a "bare metal")
· 2-nd type of hypervisor (installed
inside the OS) 2-nd type
· Hybrid hyperisor
Also divided into 2 types by type of architecture:
· Monolithic
· Microkernel
Figure 2.6 - Types of hypervisor
2.3.1 Hypervisors by type of
architecture
Hypervisors monolithic architectures
include drivers hardware devices in code. Monolithic Hypervisor located in a
single layer which also includes most of the desired components, such as core,
device drivers and I / O stack. This approach used by VMware ESX and
traditional mainframe systems. Figure 2.7 shows the architecture of a
monolithic hypervisor.
Figure 2.7 - Architecture of monolithic hypervisor
to Figure 2.7 in a monolithic model - the hypervisor
uses its own drivers to access the hardware . Guest operating systems run on
virtual machines over of the hypervisor. When the guest needs access to the
equipment, it must pass through the hypervisor and its driver model. Usually
one of the guest operating system plays the role of an administrator or a
console, which starts a component for provisioning, management and monitoring
of all guest operating systems running on the server. The most common example
is a monolithic architecture VMware ESX. As shown in Table 2.1, monolithic
architecture has its own advantages and disadvantages. Among the advantages:
· Increased (theoretically)
performance because of the drivers placed in the space of the hypervisor,
· Increased security, as
undesired operation of management of the OS (in terms of VMware - «Service
Console») will not result in the failure of all running virtual machines.
Disadvantages monolithic architecture following:
· Handle equipment which
drivers are available in the hypervisor
· Potentially lower security - due to
the inclusion in the hypervisor arbitrary code in the form of device drivers,
· Sustainability - if an
updated driver has bug, it cause crash in the whole system, in all its virtual
machines.
2.1 - Disadvantages and advantages of
hypervisor.
|
Advantages
|
Disadvantages
|
|
Increased performance
|
|
Increased security
|
Potentially lower security
|
|
Poor stability if driver has an
error
|
Micronucleus hypervisor uses a very thin, specialized
hypervisor that only performs the core tasks of ensuring partition isolation
and memory management. This layer does not include I / O stack or device
drivers. This is the approach used by Hyper-V. In this architecture, the
virtualization stack and device-specific drivers are located in a special
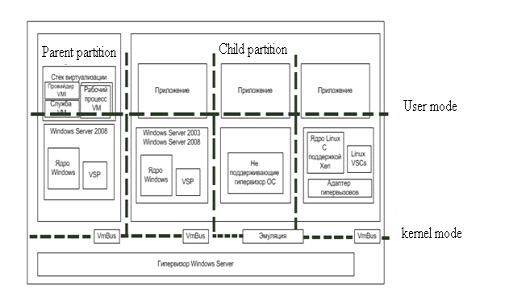
section of the OS,which called the parent partition, as shown in Figure 2.8.
Figure 2.8 - Architecture of
microkernel hypervisor
microkernel implementation use
"thin hypervisor". In this case it does not have drivers. Instead,
the drivers work in each individual section to any guest OS was able to get
through the hypervisor access to the equipment. With this balance of power,
each virtual machine occupies a separate section, which has a positive impact
on the security and reliability. In a microkernel hypervisor model (used in the
virtualization of Windows Server 2008 R2), one section is the parent (parent),
the rest - a subsidiary (child). Section - is the smallest isolated unit,
supported by the hypervisor. Size Hyper-V hypervisor less than 1.5 MB, it can
fit on one 3.5-inch floppy disk. Each partition is assigned a specific
hardware resources - share of CPU time, memory, and other devices. The parent
partition creates child partitions and manage them, and also contains a stack
virtualization (virtualization stack), used to control the child partition. The
parent partition is created first and owns all resources that do not belong to
the hypervisor. Possession of all the hardware resources means that it is the
root (ie, parent) section controls the supply connected Plug and Play device in
charge of hardware failures and even controls the loading of the hypervisor.the
parent partition contains a virtualization stack - a set of software components
located on top of the hypervisor and together with him supporting virtual
machines. Virtualization stack communicates with the hypervisor and performs
all the functions of virtualization that are not supported directly by the
hypervisor. Most of these functions is associated with the creation of child
partitions and manage them and necessary resources (CPU, memory,
devices).compared with a monolithic hypervisor approach is that the drivers that
need to be located between the parent partition a physical server and do not
require any modification to the driver model. In other words, the system can
simply apply the existing drivers. In Microsoft chose this approach because the
need for new drivers braked heavily to the development of the system. As for
the guest operating system, they will work with emulators or synthetic
devices., the main priority was security, so for most companies is acceptable
will be a couple of percent loss in productivity in order to reduce the front
of attack and improve stability.
2.3.2
Hypervisors by type of running
First type of hypervisor runs on the
hardware and manages independently. Guest OS running in virtual machines are
located above the level, as shown in Figure 2.9.
Рисунок 2.9 - First type of Hypervisor
of the second type runs in one ring with the main OS
kernel. Guest code can be executed directly on the physical processor, but
access to the input-output devices of the computer guest OS through the second
component, the normal process of the main OS - Monitor user level as shown in
Figure 2.11
 2.11
- Hypervisor of second type
2.11
- Hypervisor of second type
:MicrosoftVirtualPC,VMwareWorkstation,QEMU,Parallels,
VirtualBox.2.12 shows hypervisor first type and hypervisor of the second type,
which clearly shows the difference in the absence of a hypervisor for operating
the first type, which means that the second type of hypervisor is installed
directly on the physical computer components.
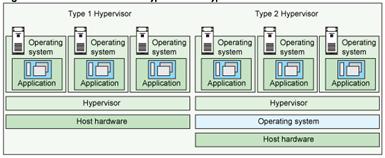
Figure 2.12 - Difference between
first type and second type of hypervisor
Hybrid hypervisor consists of two parts: a thin hypervisor
that controls the processor and memory, as well as working under its control
special service running in the ring reduced level. OS service through guest OS
access to physical hardware.
2.4 Overview of virtualization
platforms
2.4.1 Virtualization platform - VMware
The company VMware - one of the first players in the market
of virtualization platforms. In 1998, VMware has patented its technology and
virtualization software has since released many effective and professional
products for virtualization at various levels: from VMware Workstation,
designed for desktop PCs, to VMware ESX Server, enabling enterprises to
consolidate physical servers to virtual infrastructure. VMware will have the
following products: VMware Workstation, VMware Player, VMware Server, VMware Ace,
VMware vSphere, VMware vCenter, Server VMware VMmark, VMware Capacity Planner,
VMware View, VMware ThinApp, VMware vCenter, VMware vSphere Hypervisor, VMware
ESX Server.Workstation - platform, focused on desktop-users and intended for
use by software developers, and IT professionals. As the host operating systems
supported Windows, Linux, Mac and others. Can be used in conjunction with the
development environment that makes it particularly popular among developers,
trainers and support technicians. With VMware workstation, you can create
complex virtual machines on laptops with the decision Cloud Foundry, work with
applications to process large volumes of data and 64-bit VM in vSphere
environment or Microsoft Hyper-V Server.Player - free "player" of
virtual machines based on the virtual machine, VMware Workstation, designed to
run a ready-made virtual machine images created in other products of VMware, as
well as Microsoft VirtualPC and Symantec LiveState Recovery. Starting with
version 3.0 VMware Player allows you to create virtual machine images. Limited
functionality is now mainly concerns the functions intended for
IT-professionals and software developers.product VMware Server is a pretty
powerful virtualization platform, which can be run on servers running host
operating systems Windows and Linux. The main purpose of VMware Server -
support for small and medium-sized virtual infrastructure of small businesses.
Due to the low complexity of its development and installation, VMware Server
can be deployed as soon as possible, both on the servers of the organizations,
and on home computers.Ace - product to create secure virtual machine security
policies, which can then be spread on the model of SaaS
(Software-as-a-Service).vSphere - range of products, which is a reliable
platform for data center virtualization. The company is positioning this
complex as well as a powerful virtualization platform for building and
deploying private "clouds". VMware vSphere is available in several
editions with features designed specifically for small companies and
medium-sized companies and corporations.
 2.13 Structure of vShpere.
2.13 Structure of vShpere.
ESX Server - is a hypervisor which partition a physical
server into multiple virtual machines. VMware ESX is the foundation of VMware
vSphere package and is included in all editions of VMware vSphere.
 2.14
Hypervisor VMware ESX.
2.14
Hypervisor VMware ESX.
2.4.2 Virtualization platform - Microsoft
Microsoft Virtual Server. Server virtualization platform Microsoft
Virtual Server can be used on a server running Windows Server 2003 and is
designed to simultaneously run multiple virtual machines on a single physical
host. The platform is free and provides only the basic functions.Virtual PC.
Product Virtual PC was bought by Microsoft in conjunction with the company and
Connectix first branded Microsoft released as Microsoft Virtual PC 2004.
Virtual PC and purchasing company Connectix, Microsoft has built a far-reaching
plans to provide users with a tool to facilitate the migration to the next
version of the Windows operating system . Now Virtual PC 2007 is free and
available to support desktop operating systems in virtual machines.Hyper-V.
Microsoft product is positioned as the main competitor to VMware ESX Server in
enterprise virtualization platforms. Microsoft Hyper-V is a solution for server
virtualization based on processors with x64 architecture in enterprise
environments. Unlike a Microsoft Virtual Server or Virtual PC, Hyper-V provides
virtualization at the hardware level, using virtualization technology built
into the processor. Hyper-V provides high performance, almost equal to the
output of one operating system running on a dedicated server. Hyper-V is
distributed in two ways: as part of Windows Server 2008, or as part of an
independent free product Microsoft Hyper-V Server.Windows Server 2008 Hyper-V
technology can be deployed as a full installation and operation in Server Core,
Hyper-V Server only works in the Core. This allows you to fully realize the benefits
of a "thin", economical and manageable virtualization platform.V is
an integrated component of the 64-bit versions of Windows Server 2008 Standard,
Windows Server 2008 Enterprise and Windows Server 2008 Datacenter. This
technology is available in 32-bit versions of Windows Server 2008, Windows
Server 2008 Standard without Hyper-V, Windows Server 2008 Enterprise without
Hyper-V, Windows Server 2008 Datacenter without Hyper-V, in Windows Web Server
2008 and Windows Server 2008 systems based on Itanium.
 2.15 - Architecture of Hyper-V
2.15 - Architecture of Hyper-V
versions of the Hyper-V have one parent partition. This
section controls the functions of Hyper-V. From the parent partition console
runs Windows Server Virtualization. In addition, parent partition is used to
run virtual machines (VM), supports streaming emulation of old hardware. Such
VM, built on templates, emulating hardware, are analogues of VM, working in a
product-based virtualization host, such as Virtual Server.Гостевые VM запускаются из дочерних разделов Hyper-V. Child partitions
support two types of VM: high performance VM-based architecture VMBus and VM,
managed host system. The first group includes a VM with Windows Server 2003,
Windows Vista, Server 2008 and Linux (supporting Xen). New architecture
features a high-performance VMBus conveyor operating in RAM, connecting clients
Virtualization Service Clients (VSC) on the VM guest with the provider Virtual
Service Provider (VSP) host. VM, managed host, launch platforms that do not
support the new architecture VMBus: Windows NT, Windows 2000 and Linux (without
the support of technology Xen, such as SUSE Linux Server Enterprise 10).System Center
Virtual Machine Manager (SCVMM) - separate System Center products for virtual
infrastructure management, efficient use of resources of physical nodes, as
well as facilitate the development and creation of new guests for
administrators and users. The product provides full support to consolidate
physical servers to virtual infrastructure, fast and reliable conversion of
physical machines to virtual, virtual workloads reasonable accommodation in
appropriate physical nodes and a single console for resource management and
optimization. SCVMM
provides the following features:
· Centralized management of servers
virtual machines across the enterprise. SCVMM supports management of servers
Microsoft Hyper-V, Microsoft Virtual Server, VMware ESX, and in the future
there is support for Xen.
· Create a library of templates of
virtual machine. Virtual machine templates are predefined sets of images of
operating systems that can be deployed in minutes.
· Migration (converting) physical
servers to virtual machines - the technology P2V. P2V technology allows to make
the transfer of a physical server to a virtual non-stop work. Thus, there is a
possibility of the whole online backup server and in case of its failure, it is
possible for one minute to start the virtual server and continue.
· Cluster Management of Hyper-V.
2.4.3 Платформа Microsoft Azure
Platform Microsoft Azure - a model of
Platform as a service that provides the opportunity to develop and run
applications and store data on servers located in distributed data centers.
Originally called Windows Azure. In 2014, the platform was renamed to Microsoft
Azure.
Microsoft Azure cloud fully implements two models - the
platform as a service (Platform as a Service, PaaS) and infrastructure as a
service (Infrastructure as a Service, IaaS). The efficiency of the Windows
Azure platform provides a global network of data centers Microsoft. The main
features of this model:
• payment only consumed resources;
• general, multi-threaded structure calculations;
• abstraction of infrastructure.
Рис. 2.16 The components
provided by the platform Microsoft Azure
Microsoft developed a platform Azure, allowing .NET
developers to enhance their experience of creation in Visual Studio 2008 (and
higher) ASP.NET Web applications and Windows Communication Framework (WCF)
services. Projects Web applications run in the standalone version of Internet
Information Services (IIS) 7. Web applications and Web services run in a
partially trusted security mechanism allows you to restrict access to computer
resources code (Code Access Security), which approximately corresponds to the
average level of trust and ASP.NET restricts access to certain operating system
resources. Set of development tools used Windows Azure allows full access to
the resources of the computer not to run .NET code using .NET libraries that
require full trust, and the process of interaction, using software channels
(Pipe). Microsoft promises to support the launch of the program code Ruby, PHP
and Python in the "cloud" platform. The original version of the
development platform was limited programming environment Visual Studio 2008 and
above with a plan to support the tool Eclipse. Windows Azure platform supports
web standards and protocols including SOAP, HTTP, XML, Atom and AtomPub.
Windows Azure, которая включает:
· Azure Hosted service;
· Storage Accounts;
· SQL Azure
· Live Services: existing APIs.
Live services: existing APIs are not part of the preliminary
version and does not require a token. Since early 2009, Windows Azure token
entitles you to one account Hosted Service, two accounts for Storage. You are
requesting tokens Azure across the page Microsoft Connect, which is accessed
from the portal page. The figure 2.17 shows the account page, which includes
links to the settings page and control SQL Azure, .NET services and Live
services. Live Alerts page allows you to configure how and when to receive
messages containing critical signal applications, newsletters and updates the
portal.
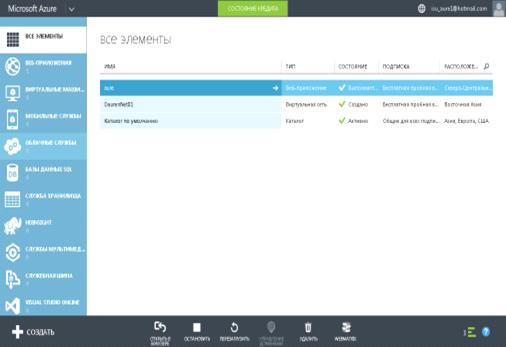
Figure 2.17 - Accaunt page
Azure
includes geolocation, which allows account holders to choose the data center
for the location of Hosted Services and Storage Accounts. For example,
USA-Northwest (Quincy, WA) and USA-Southeast (San Antonio, TX.). The user can
add and sets Hosted Services Storage Accounts in the group to ensure that the
services are located in the repository and the same data center, in order to
increase productivity.
Storage Windows Azure Storage provides developers with the
ability to store data in the cloud. Application can access their data at any
time from anywhere, store any amount of data, and as long as you want. The data
is guaranteed not to be damaged and lost. Windows Azure Storage provides a rich
set of data abstractions:
• Windows Azure Table - provides structured storage
conditions of service.
• Windows Azure Blob - provides storage for large data items.
• Windows Azure Queue - provides asynchronous work dispatch
to implement the exchange of data between services.
2.4.4 Network of virtual machines
Each virtual machine network consists of one or more virtual
subnets. Network virtual machines generates insulating boundaries within which
the virtual machines on the network can communicate with each other. As a
result, the virtual subnet a network of virtual machines should not use
overlapping prefixes IP-addresses. Each virtual machine has a network routing
domain that identifies a given network. PH domain routing (RDID), identifying a
network of virtual machines, appointed administrators or data center management
software, data center, such as System Center 2012 R2 Virtual Machine Manager
(VMM). RDID has format GUID Windows - for example
"{11111111-2222-3333-4444-000000000000}".
2.4.5 Routing outside of the virtual network
Deploying a client networks requires that network
virtualization environment Hyper-V has been linked with resources not included
in network virtualization environment Hyper-V. Gateways virtualization networks
are needed to provide communication between the two environments. Scenarios
that require the use of the gateway network virtualization Hyper-V, include a
private cloud and hybrid cloud. In the main gateway network virtualization
Hyper-V are required for virtual private network (VPN) and routing.can have
different physical form factors. They can be based on Windows Server 2012 R2,
built into the top-level rackmount switch (TOR) or load balancer, included in
other existing network devices, or be a new standalone network device.routing
in the private cloud or large enterprises can not be resolved, or for reasons
of compliance, not be able to move some of its services and data in the public
cloud hosting provider. However, enterprises want by combining the resources of
their data centers in a private cloud to get the benefits of cloud technology,
network virtualization provided by Hyper-V. When deploying a private cloud
overlap IP-address can not be required, as companies tend to have sufficient
internal space non-routable addresses (for example, 10.xxx or 192.xxx). Consider the example in Figure 2.18.
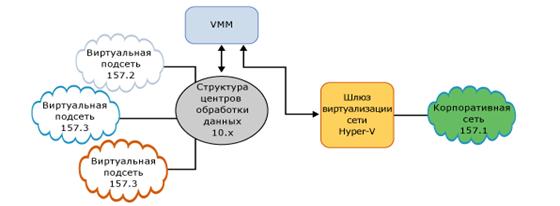 2.18 - Deploying a Private Cloud
2.18 - Deploying a Private Cloud
It
should be noted that a virtual address of the client subnet represented as
157.x. At the same IP-address in the non-network virtualization of the network
(corporate network) is also presented in the form 157.x. In this case, the
address of the supplier for virtual subnets in the data center are the
IP-addresses of the form 10.x. This deployment allows the company to take
advantage of network virtualization Hyper-V to provide flexibility as if a
virtual machine and cross-subnet live migration in the structure of the data
center. This increases the efficiency of the data center, thereby reducing both
the running costs and capital costs. In this scenario, the gateway network
virtualization Hyper-V provides routing between the IP-addresses of the form
10.x and 157.1.
Hybrid cloud (VPN type "net-net") A key advantage
of network virtualization Hyper-V - is that it allows you to quite easily
expand the local data center to data center using cloud-based Windows Server
2012.This is a hybrid model clouds. (Figure 2.19).
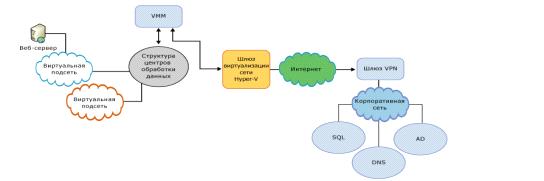 2.19. Hybrid cloud model
2.19. Hybrid cloud model
this scenario, the internal subnet containing Web servers,
moves from the enterprise network to the data center hosting provider cloud.
Taking advantage of the offer Bring Your Own IP Address (Use your own
IP-address) of the hosting provider, the company got rid of the need to modify
the network configuration of the virtual machine web server or any other
endpoint network tied to the Web server. Hoster provides a secure communication
channel through the use of the gateway network virtualization Hyper-V.
3. Algorithm works of “Cloudy” web
application
web-application to create a hybrid infrastructure is designed
to help to users in the deployment of a hybrid infrastructure step by step in
the form of labororary works. User will be granted access to the information in
the 2 modes of functionality as shown in figure 3.1:
· The registered user mode
· The unregistered user mode
Figure 2.1 - Access modes
to Figure 2.1 when user entered as “unregistered user”
(restricted access), he will be able to view laboratory work and theoretical
information.the “registered user” mode (expanded access) in addition to
functionality granted to unregistered users, the user will be available next
functions:
· The search button within the site
· List of performed laboratory work
· Comments and questions for laboratory
worksthe unwillingness to use the “unregistered user mode” by user , the user
is offered to register by entering personal data to database. Figure 2.2 shows
a diagram of adding a new user to the database and the entrance to the site
without authorization as a registered user.
 2.2
- Scheme of access to the websitethe registration, the user fills registration
form in registration page where user must indicate the name and other data.
Based on filled registration form, assigned a login and password to the user.
2.2
- Scheme of access to the websitethe registration, the user fills registration
form in registration page where user must indicate the name and other data.
Based on filled registration form, assigned a login and password to the user.
3.1 Functional of website
this informational website information divided into 2
main parts:
· theoretical material
· laboratory worksto collaboration
scheme in Figure 2.3, where shown interaction of website with database also
shown functional of website.
 2.3
- Collaboration scheme of website
2.3
- Collaboration scheme of website
To select the theoretical section, the user must select the desired
theme and click it with the mouse on it:
· Cloud computing
· Virtualization technologies
· Models of expansion of cloud
computing
· Web-services provided by cloud
computing
· Features of virtual network
User can create complete hybrid infrastructure when he
performs the laboratory works :
· Creating local infrastructure on
Windows Server 2012/2008 with Hyper-V role.
o Instrallation and setup Hyper-V
o Creation of virtual machine on
Windows Server 2012/2008.
· Creation virtual infrastructure on
Windows Azure
o Creation of virtual machines in
virtual network Windows Azure
o Deployment of virtual machine on
Windows Azure platform
o Creation of virtual network and
configure the tunnel between Windows Azure and local infrastructure
o Creation of virtual network
3.2 Software
tools
platform assembly of Web server Xampp was used as web-server
which is distributed freely according to the license GNU General Public
Licenseadvantage of Xampp is the content of the script interpreter and a large
number of additional libraries, allows you to run a full-fledged web server.
Xampp works with all 32 - 64 bit OS Microsoft.The composition of Xampp
includes: Apache ,MySQL,phpMyAdmin.program is regularly updated to include the
latest versions of the Apache/MySQL/PHP и Perl. Also in composition of XAMPP present another modules , including
OpenSSL и phpMyAdmin.HTTP-server is
cross-platform software and maintains operating systems like Linux, BSD, Mac
OS, Microsoft Windows, Novell NetWare, BeOS.
The main advantages of Apache is reliability and flexibility
of configuration. Apache allows to connect external modules to provide data,
use database for user authentication, modify the error messages and etc.Also
supports IPv6. Apache configured by using text configuration files. The main
parameters are already configured by default and will work in most cases.
Function of web-server perform software which installed on personal computer.
When browser connects to the web-server and sends header “GET”(request to send
data), Apache handles the request. Apache checks, whether there is a title GET
file, and, if so, send it along with the browser title.
As DBMS(database management system) was used MySQL. MySQL is
a highly productive, reliable database management system that integrates well
with PHP and is focused on the implementation of dynamic web applications.
Figure 2.5 - Architecture of DBMS
MySQL allows to database developers and administrators to create advanced web, cloud and
embedded applications that can handle the ever-increasing amounts of data.program code for
implementation of application has been selected one of the most popular
languages for implementing web applications - PHP.is extremely important factor
in the programming for multi-user environments, which include web. A very
important advantage of PHP is its "engine". "The engine» PHP is
neither the compiler nor the interpreter. He is the transmitting interpreter.
Such a device "engine» PHP script allows processing at a sufficiently high
speed. Popularity in building web sites is determined by the presence of a
large set of built-in tools for developing web applications. The main ones:
· Automated extraction of POST and
GET-parameters and environment variables of Web server in predefined arrays;
· Interaction with many different
database management systems;
· Automated sending HTTP-headers;
· work with HTTP-authorization;
· work with cookies and sessions;
· Work with local and remote files,
sockets;
· processing of files uploaded to the
server;
4. Justification of the
cost-effectiveness of the project
aim of the diploma project is the development of educational
and informational web site, based on cloud computing. This section examines the
degree project site development from an economic point of view.efficiency - it
is possible to obtain maximum benefits from the resources available. To do
this, you need to constantly relate benefits (benefits) and the costs or, to
put it differently, behave rationally. Rational behavior is that the producer
and the consumer goods strive for the highest efficiency and to maximize the
benefits of this and minimize costs.important part of the economic system
efficiency is the efficiency of capital investments. It is expressed by the
ratio of the obtained effect to capital investments that caused this effect.
Capital efficiency is measured set of indicators, which includes the overall
effect of capital investments, the rate of return, payback period, comparative
effectiveness, and others. The indicators of economic efficiency of capital
investments are used to compare alternative investment projects and select the
best project.large role in the economic process (ie, whether economical
software product or not) depends on the programmers have created this software.
You play the role of the creation, debugging, and program.
4.1 Calculating the cost of
materials
install the server part of the software package and necessary
to organize one job for a programmer with a computer or laptop. During the
design phase of the server has been installed in the workplace programmer to
reduce costs. To solve workplace, it was decided to use a laptop of brand
Lenovo model Y580 (processor Intel Core i7-3610QM 2.3 GHz; video card NVIDIA
GeForce GTX 660M - 2048 MB, 8192 MB RAM, DDR3 SDRAM) price which is 163290KZT.
In addition in the process of developing a web site following materials were
used:
• USB Flash Drive 8 GB - 3000KZT.
• Pens, pencils - 500KZT.
• Office paper size A4 - 500 KZT.expenditure on materials is:
167 290 KZT.
4.2 Costs to wages
basic wage is calculated from the Developer salary as well as
the duration of individual stages of work in the development of software
system, taking into account the quality, complexity and working conditions. The
table shows the programmer salary in the field of web development in the past
month. The average number of working days in a month is 22 days.
.
Table 4.1 Staffing the project team
|
№
|
Position
|
Salary (KZT/ per month.)
|
|
1
|
Programmer
|
150 000
|
|
Total
|
150 000
|
Additional monthly payment shall be at the rate of 15%
of basic salary and will be: KZT. (4.1)
KZT. (4.1)
Accrual of social insurance bodies
in wages make up 20% of the basic salary: KZT. . (4.2)to the plan, the creation of a web site has been divided into
several stages. Number of days worked to create a website of 44 full working
days. Table 4.2 shows the steps and the number of days are designed to perform
a certain stage.
KZT. . (4.2)to the plan, the creation of a web site has been divided into
several stages. Number of days worked to create a website of 44 full working
days. Table 4.2 shows the steps and the number of days are designed to perform
a certain stage.
4.2
Stages
|
Stage
|
Pre-project research
|
Development and coordination of
design
|
Software part of the project
|
Site content
|
Site testing
|
Delivery site in operation
|
|
Number of days to perform stage
|
5-days
|
7-days
|
19-days
|
5-days
|
3-days
|
5-days
|
total amount of the payment to the employee, including
additional earnings and insurance is shown in Table 4.3.
4.3 Cost of basic and additional salary
|
Position
|
Salary (tenge per month.).
|
Number of days worked
|
Salary tenge per month.).
|
Sum (KZT)
|
Additional salary (KZT)
|
Social
insurance (KZT)
|
Total (KZT):
|
|
Programmer
|
150 000
|
44
|
6818,18
|
300000
|
45000
|
60000
|
405000
|
4.3 Expenditure for maintenance and
equipment maintenance
of software system was made on the laptop brand Lenovo Y580
model, the price of which is 163290tg.cost of 1 hour of computer time is
calculated as follows:
h = So / Tc*Ku. (4.3)
Where  -
annual operating costs;c - annual fund-time useful PC;u -
coefficient of usage PC (0.7);operating costs are calculated according to the
formula:
-
annual operating costs;c - annual fund-time useful PC;u -
coefficient of usage PC (0.7);operating costs are calculated according to the
formula:
o
= Sa+ Sm (4.4)
Where  -
deductions for depreciation (12.5% of the PC);m - maintenance costs
(2% of PC).
-
deductions for depreciation (12.5% of the PC);m - maintenance costs
(2% of PC).
So = 20411тг + 3265тг = 23676тKZT (4.4)
20411тг + 3265тг = 23676тKZT (4.4)
Fund useful operating time is calculated as the
product of the number of working days per year for the duration of the PC in
the day: hour.cost of one hour of computer time:h.
= 23676/1764* 0.7 = 9,4KZT (4.5)of working time spent on development and
debugging software package was (44 * 8) = 352 hours. Thus, the cost of
maintenance and operation of the PC are:
hour.cost of one hour of computer time:h.
= 23676/1764* 0.7 = 9,4KZT (4.5)of working time spent on development and
debugging software package was (44 * 8) = 352 hours. Thus, the cost of
maintenance and operation of the PC are:
 352 *
9,4 = 3300KZT. (4.6)
352 *
9,4 = 3300KZT. (4.6)
Таблица
4.4 Смета затрат
|
№
|
Wages
|
Sum, KZT.
|
|
1
|
Expendable materials
|
167290
|
|
2
|
The costs of maintenance and
operation of equipment
|
3300
|
|
3
|
The basic wage
|
300 000
|
|
4
|
Additional salary
|
45 000
|
|
5
|
Charges to
social security payroll
|
60 000
|
|
Total:
|
557 590
|
Payback information website will be at the expense of
advertising banner from cloud providers and others. The site was created 4
places for advertising banner with the size of 200x300 pixels. Price on
advertising is shown in Table 4.5
Таблица
4.5 - Price list of advertising on website
|
3 m.
|
1 year
|
|
Adding advertising 200х300pixels on website
|
25 000 KZT
|
100 000 KZT
|
|
|
|
|
Revenue for 2 years at advertising product is equal to 800
000KZT. Payback site through advertising achieved 16.7 months.for advertising
for one month 25,000 * 4/3 = 33333,3KZT.site in months 557 590 / 33,333.3 =
16.7 months.to this application development need in the general amount of 557
590tg. From the point of view of the economy is efficient and pays off, so it
is advisable to its implementation.
5. Safety
and labor protection
Health and Safety - the science of maintaining the health and
safety for human habitat. This is achieved by the detection and identification
of dangerous and harmful factors, the development of methods and means of
protecting people from their impact in terms of life and production methods and
protection of people in emergency situations, as well as measures to eliminate
the consequences of such situations.
5.1 Characteristics
of the workplace
In this section basic information about occupational safety
and health was covered for place where diploma project was implemented. If be
exact the field of practice was computer laboratory. This room is located in
the building of International University of Information Technology (IITU).:
International University of Information Technology.
Address: Almaty city, Dzhandosov street 8“A”.building is
located in the administrative part of the city, Almalinskiy district.area: 8578
m2.of Employees: 250.
This computer laboratory is one of the many training rooms
which are equipped approximately with 10 personal computers (PC).of computer
laboratory:- 7 meters , Length - 10 meters , Height - 2.5 metersbuilding of the
university is ten-story building. And this building corresponds to its
functional purposes and to the requirements for safety and health. Computer
laboratory which was field for practice in located in fourth floor of the
building. It has a window opening on the southeast side and the front door is
to opposite side.equipment: 10 computers, 1 projector, 1 server.the laboratory
has the air conditioning, heating and automatic fire alarm systems.
5.2 Analysis of dangerous and
harmful factors
working in front of the computer some harmful and dangerous
factors influence to people. These factors can be:
Electromagnetic fields and radiation
Insufficient level of illumination
Increased noise levels
Electrostatic fields
Emotional overloadof these factors in the one way to
influence to the health of human. Finally it can be reason for headaches,
fatigue, and eyesight. After that human become less productive. That is why
that condition for labor in enterprise is one of the important items which have
to keep certain rules.
5.2.1 Production sanitation and
health
Properly designed and executed industrial lighting improves
visual work, reduces fatigue, increases productivity, beneficial effects on the
production environment, providing a positive psychological impact on the
worker, increases safety and reduces injuries.[8]
5.2.2 Lighting
Wrong direction of light in the workplace can create harsh
shadows, reflections, disorient worker. There are three types of lighting -
natural, artificial and combined (both natural and artificial together).The
laboratory used artificial lighting.[12]lighting is used when working at night
and during the day when you cannot provide the normalized values of the natural
light (cloudy weather, short daylight hours). Lighting, in which the lack of
standards for natural lighting is complemented by artificial lighting, is
called a combined[12]
5.2.3 The parameters of the
microclimate
Microclimate parameters can vary widely, while a necessary
condition of human life is to maintain a constant body temperature through
thermoregulation, i.e. ability to regulate heat output into the environment.
Principle of regulation of microclimate - the creation of optimal conditions
for heat exchange of the human body and the environment.The supply rate of
fresh air in the room where the computers are given in Table 8.
In the laboratory temperature of 23 ° C and 50% relative
humidity.In areas where the developed software system is provided with natural
ventilation. To ensure comfortable conditions are used as methods of organization
(the rational organization of the work, depending on the time of day and year,
the alternation of work and rest)
10 - Rates of fresh air in the room where the computers
|
Characteristicsoftheroom
|
Air flow supplied into the room
fresh air m3 / in per person per hour
|
|
Volume up to 20m3 per person
|
Atleast 30
|
|
20 ... 40m3 perperson
|
Atleast 20
|
|
More than 40m3 per person
|
Naturalventilation
|
5.2.4 Noise and Vibration
The noise degrades the conditions providing the harmful
effects on the human body. Working in conditions of prolonged noise exposure
experienced irritability, headaches, dizziness, memory loss, fatigue, loss of
appetite, pain in the ears, etc. Table 8 shows the maximum sound levels
depending on the category of severity and intensity of labor, which are safe
with respect to maintaining health and performance.the laboratory, the noise
level is defined as a little tense. Noise level in the workplace mathematicians,
programmers and operators of video should not exceed 50dBA, and in the halls of
the information processing on computers - 65dBA.[14]
5.2.5 The electromagnetic and
ionizing radiation
Most scientists believe that a both short-term and long-term
effect of all forms of radiation from the monitor screen is not dangerous for
health personnel serving computers. However, comprehensive data about the
dangers of exposure to radiation from the monitors on working with computers
did not exist, and research in this area continues. Maximum ray workplace
computer operator usually does not exceed 10mkber / h, and the intensity of
ultraviolet and infrared radiation from the screen of the monitor is within
10..100mV/m2.
5.2.6 Ventilation
Ventilation - a set of interconnected devices and processes
designed to create an organization of ventilation, consisting in the removal of
contaminated industrial premises or superheated (cooled) air supply instead of
clean and cold (hot air), allowing you to create a working area favorable air
environment.on the movement of air and clean room ventilation is divided into
an artificial (mechanical), and a natural combination. The laboratory used form
of mechanical ventilation. If ventilation air is generated by mechanical
devices - fans and other thermal pressure difference created by the balance
column of air inside and outside the premises. Thus, a pressure differential
causes air. Wind pressure due to the action of wind, by which on the windward
surface of the building there is a positive pressure on the leeward side of a
depression.
5.3 Health and safety during the
work
.3.1 Requirements for safety before
starting work
There have to be requirements before work and it does not
depend on type of work. This restrictions and notifications will help to get
rid of dangerous consequences and harmful factors. Some restrictions before
working in computer laboratories:
- In the computer lab is not allowed to
work in street clothes, noise, smoking, eating.
- Do not obstruct aisles, exit
corridors and access to fire.
- For each computer user group can
operate no more than two people.
- The user must ensure that no visible
damage to the computer (i.e. violation of hull integrity , insulation failure
in cables , faulty display power- voltage signs on the body , etc.). Never
operate the computer with the case open.
5.3.2 Requirements for safety during
working with PC
In the automated system management where main actions made by
human, visualization of information on the screen plays big role. Because the
size of information which users can reach or understand depends on from this
factors. is why we have to define requirements for devices which demonstrates
information:
- Screen has to be located from eyes in
distance 400 x 800 mm and in the middle of view sight.
- The top sight of the screen has to be
placed on height 750 mm from the surface of the chair.
- The distance between keyboard and
edge of table should be approximately 60mm. Height of the keyboard does not
have to be over than 50 mm. The preferable angle of slope is 150.have to
correspond to the next technical requirements listed below:
- Brightness not less than 100
luminosity per meter square.
- The minimum size of lighting dots -
not over than 0.4 for monochromic screens and not above than 0.6 for colored
screens.
- Number of dots per line - not less
than 640.
- Low-frequency jitter in the range 0.5
+/- 1.0 Hz must be located within 0.1mm.
- Screen must have anti- glare
function.
- Observe the optimal distance between
the eyes and the monitor screen (60- 70 cm);
- Perform comply with sanitary norms
and modes of work and leisure;
- Observe the rules of operation of
computer technology in accordance with the instruction manual;
- Observe the rules of fire safety;
5.4 Health and safety during
emergency
safety - system of organizational measures and technical
means to prevent the harmful and dangerous effects on the operation of the
electric current and the electric arc. In the workplace, place the monitor,
keyboard, system module. Because their work is used alternating current and
voltage of 220 volts. In this respect, it should meet the requirements for
electrical safety.protection of buildings - a set of technical solutions
adopted in accordance with the instructions. The building of the International
University provides internal and external lightning protection system of the
building.disappearance of the compound is intentional electrical conductive
parts of electrical installations with grounded neutral point of the generator
or inverter in three-phase systems with a grounded single-phase AC power output
from a point source based in the DC networks to be carried out to to electrical
safety.in the laboratory, can lead to very negative consequences (loss of
valuable information, property damage, death, etc.), so you must: identify and
eliminate all causes of fire, develop an action plan to eliminate a fire in a
building evacuation plan building.safety - is the state of the object, which is
characterized by the ability to prevent the emergence and development of the
fire, and the impact on people fire hazards.of fire:
• wiring, outlets and switches that could cause a short
circuit or insulation breakdown;
• Use of damaged (defective) devices;
• internal use electric heaters with open heating elements;
• The risk of fire due to lightning in the building;
• inflammation of the building due to external
influences;safety - a complex of organizational and technical measures aimed at
providing good security people on the prevention of fire, limiting its spread
and to create conditions for effective fire extinguishing. As fire prevention
is extremely important to the correct assessment of the fire building, hazard
identification and alignment of the ways and means of fire safety and
protection. One of the conditions for fire safety - eliminating possible
sources of ignition. This is very dangerous for the computer and the
developer.handling of fire and failure measures to comply with fire
safetywatched fire mode, which defines the rules of human behavior, organization
of educational process and service facilities to ensure fire safety
requirements.determining the terms of fire safety at the University of
identified:
• smoking area;
• the place and the maximum amount of raw materials,
flammable and combustible liquids and hazardous substances;
• procedure for cleaning dust and combustible waste;
5.5 Engineering calculations
Light calculation job is to choose the lighting system, the
definition of the required number of fixtures, type and placement. On this
basis, we calculate the parameters of the artificial lighting.
5.5.1 Light calculation
The calculation is performed for lighting rooms of 15m2, with
a width 5m, height - 3 m use the method of flux.
To determine the number of lamps define the luminous
fluxincident on the surface by the formula:
 (4.1)
(4.1)
- Calculated luminous flux lm;- Normalized minimum
illumination, Lk (determined by the table). Programmer's job, according to this
table can be classified as precision work, therefore, the minimum illumination
will be E = 300Lk;- The illuminated area of the room (in this case S = 15m2);-The
ratio of average brightness to the minimum (usually taken to be 1,1.1,2, let Z
= 1, 1);
К -
factor of safety, taking into account the reduction in light output light
fixtures as a result of contamination during use (it value depends on the type
and character space held therein works and in this case K = 1.5);- Utilization
rate (expressed as the ratio of the light flux incident on the calculated
surface to the total flux of all lamps and is calculated as a fraction of a
unit, depending on the characteristics of the lamp, the size of the room,
painting walls and ceilings, which are characterized by reflection coefficients
of the walls (Рs) and ceiling (Рp)), value of the coefficients Рs and Рp have been mentioned above: Рs=40%, Рp=60%.value of n is defined
by the table of coefficients using different fixtures. To do this, we calculate
the index space by the formula:
 (4.2)
(4.2)
-Room space, S = 15 m2;-Rated altitude of
suspension, h = 2.92 m;
А
-Width of the room, А = 3 m;
В
-Length of the room, В = 5 m.the values we get:
 the index premises I, we find n = 0,22substitute all the
values in the formula for determining the luminousflux F:
the index premises I, we find n = 0,22substitute all the
values in the formula for determining the luminousflux F:
 fluorescent lighting, select the type LB40-1, the luminous
flux which F = 4320 Lk.Calculate the number of lamps required by the formula:
fluorescent lighting, select the type LB40-1, the luminous
flux which F = 4320 Lk.Calculate the number of lamps required by the formula:
 (4.3)
(4.3)
-Determined by the number of lamps;-Luminous flux, F = 33750
Lm;l-light stream of a lamp, Fl = 4320 Lm.
 choosing lighting luminaries use ML. Each
lamp comes with two lamps.
choosing lighting luminaries use ML. Each
lamp comes with two lamps.
5.5.2 Calculation of noise
One of the negative factors working environment at the ITC is
a high level of noise generated printing systems of air conditioning equipment,
fans cooling systems in computers themselves.order to address the need for and
feasibility of noise reduction is necessary to know the noise levels at the
operator. The noise level arising from a few incoherent sources operating at
the same time, calculated on the basis of the principle of energy summation of
individual radiation sources:
 (4.4)
(4.4)
i -sound pressure level of the i source;- The number of noise
sources.this sound pressures will maximum this is very dangerous to developer earns,
because many noise is hazardous to peoples.operator station is equipped with
the following equipment: hard drive in the system unit, the fan (s) cooling PC,
monitor, keyboard, printer and scanner. Substituting the values of sound
pressure level for each type of equipment in the formula, we get:
∑=10·lg(104+104,5+101,7+101+104,5+104,2)=49,5
dB.
when you consider that it is unlikely peripherals such as a
scanner and a printer will be used at the same time, this figure would be even
lower. In addition, if the printer is not necessarily the immediate presence of
the operator.
Conclusion
diploma project is dedicated to developing an informational
web-application for deploying hybrid infrastructure.the programming the fully
working functional application was developed, where stored theoretical material
and assembled laboratory works .works was realized by using Windows Server
2008R2/2012R2, Hyper-V virtualization, Windows Azure and was published by the
link cloudy.kz.section contains review of the cloud computing technology,
service models(SaaS, PaaS, IaaS) and deployment models(private cloud, public
cloud, hybrid cloud) of cloud computing, advantages and disadvantages of types
of deployment models cloud computing, and the safety information on clouds.section
contains the whole information about technology of virtualization including
types virtualization resources(association, aggregation and concentration of
components, grid computing, partitioning, encapsulation), types virtualization
of platforms(Full emulation (simulation), paravirtualization, application level
virtualization, operating system-level virtualization, virtualization address
space) and hypervisor and his types(Monolithic, microkernel, 1-rst type of
hypervisor (established on a "bare metal") , 2-nd type of hypervisor
(installed inside the OS) , hybrid hyperisor).section contains algorithm of
web-application which I named as “Cloudy”. Described functional of website and
software tools which used in creating web-application.section presents economic
justification and benefits of using the product developed on cloud
computingsection provides for the Labor protection and Industrial
Ecology.developing of program complex main attention was focused on the user
experience and user friendly interface. The objectives of the diploma project
have been made in full.
References
1
Federov A. G. Martinov D. N. Windows Azure Platform [ Электронный ресурс ] - Режим доступа
к журн. :
http://download.microsoft.com/documents/rus/msdn/Windows_Azure_web.pdf
IAAS,PAAS,SAAS
explained complained [ Электронный ресурс ] - Режим доступа
к журн. :
http://apprenda.com/library/paas/iaas-paas-saas-explained-compared/
Tejaswi
Redkar Windows Azure Platform [ Электронный ресурс ] - Режим доступа к журн. : http://it-ebooks.info/read/1033/
D.
L. Petrov Optimal algorithm for data migration in scalable storage clouds - ,
180-197
5 Theoretical Foun. of Life Safety [ Электронный ресурс ] - Режим доступа к журн. : http://userdocs.ru/geografiya/16692/index.html
Lighting jobs [ Электронный ресурс ] - Режим доступа к журн. : http://bargu.by/2991-laboratornaya-rabota-2-osveschenie-rabochih-mest.html
7
Dubovsev V.A.Life Safety - A manual for graduate students. - Kirov: ed. KIRPi
-1996
Motuzko
F.Y. Occupational safety and health-:1998. - 336p.
9
Life safety. /Under red. N.A.Belov -Znanie, 2000 - 364p.
10 Самгин
Э.Б. Освещение рабочих мест. - М.: МИРЭА, 1989. - 186с.
11
Handbook for the design of electric lighting. / Under red. G.B.Knorring. -
Energy, 1976.
Control
: Directory/ E.Y.Udin, L.A. Borisov; Under gen. red. E.Y. -Engineering, 1985. -
400p., us.
.Official
website of Windows Azure platform [ Электронный ресурс ] - Режим доступа к журн. :
http://windowsazure.com
14 Бесплатная
электронная книга «Введение в System Center 2012 R2»
[ Электронный
ресурс ] - Режим доступа к журн. : http://blogs.technet.com/b/rutechnews/archive/2014/01/13/171-system-center-2012-r2-187.aspx
.Official website of CSS [ Электронный ресурс ] - Режим доступа к журн. : http:// cssdesignawards.com
. Official website of Gliffy [ Электронный ресурс ] - Режим доступа к журн. : http://www.gliffy.com
17
John W. Rittinghouse, James F. Ransome - «Cloud Computing Implementation,
Management, and Security»
Robert
Larson , Janique Carbone - «Windows Server 2008 Hyper-V Resource Kit»
Джордж Риз - «Cloud Application Architectures»
20 Трудовой кодекс Республики Казахстан. Астана, Акорда, 15 мая 2007 года
№ 251-III ЗРК (с изменениями и дополнениями по состоянию на 17.01.2014).
(Закон Республики Казахстан от 28 февраля 2004 года №528 «О безопасности
и охране труда» признан утратившим силу с момента введения в действие Трудового
кодекса Республики Казахстан).
Санитарные правила «Санитарно-эпидемиологические требования к
эксплуатации и персональных компьютеров, видеотерминалов и условиям работы с
ними», утвержденные приказом Министра здравоохранения Республики Казахстан от
25 апреля 2011 года № 217.
22 Санитарные
правила «Санитарно-эпидемиологические требования к условиям работы с
источниками физических факторов (компьютеры и видеотерминалы), оказывающие
воздействие на человека», утвержденные приказом Министра здравоохранения
Республики Казахстан от 1 декабря 2011 года № 1430.
23 Санитарные правила «Санитарно-эпидемиологические требования к
обеспечению радиационной безопасности», утвержденные Правительством Республики
Казахстан от 3 февраля 2012 года № 202.
Закон Республики Казахстан «О гражданской защите» от 11 апреля
2014 года № 188-V (Закон Республики Казахстан от 22 ноября 1996 года «О
пожарной безопасности» признан утратившим силу с момента введения в действие
Закона «О гражданской защите»).